6.0.3.1 - Broke my webserver
- Thread starter jaydeel
- Start date
You are using an out of date browser. It may not display this or other websites correctly.
You should upgrade or use an alternative browser.
You should upgrade or use an alternative browser.
Please elaborate: how many things will likely be broken by this? Pushover notifications as well?Just a heads up. All tested customizations using HTTP Interface and JSON Interface calls are not working.
I haven't taken time yet to debug this. I just reverted to 6.0.2.10.
(and yes I did reboot the server after updating)
Can I presume you have sent off a support request to Ken?
This is new "security" features noted in the changelog.
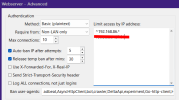
Most likely you are getting hit by the "User-Agent" string validation which by default will block anything that does not pretend well enough to be a normal web browser.
I already sent Ken a support request asking to skip those new validation functions for local/LAN addresses as that should resolve the majority of 3rd-party integration issues. But unless Ken walks back this entire set of security features, you can expect it to continue causing pain when accessing via an address which Blue Iris does not recognize as local.
Most likely you are getting hit by the "User-Agent" string validation which by default will block anything that does not pretend well enough to be a normal web browser.
I already sent Ken a support request asking to skip those new validation functions for local/LAN addresses as that should resolve the majority of 3rd-party integration issues. But unless Ken walks back this entire set of security features, you can expect it to continue causing pain when accessing via an address which Blue Iris does not recognize as local.
I did not test the Pushover curl Action before reverting back to 6.0.2.10.Pushover notifications as well?
But based on bp2008's comments, I doubt it's affected as it does not involve BI HTTP or JSON commands.
Pushover notifications still work. I also got the webserver to work by adding my external IP address to the "Limit access by IP address:" field.I did not test the Pushover curl Action before reverting back to 6.0.2.10.
But based on bp2008's comments, I doubt it's affected as it does not involve BI HTTP or JSON commands.
Mine was working fine on running Chrome my MacBook and iPhone, but I did notice that the monitor in my kitchen was having issues. It's running UI3 via Chromium on a RPI.Hmmm, mine is working fine using Zero tier.
reotto
n3wb
This change definitely breaks the Home Assistant integration. I’m logging an issue with them, but reverted back.
bctrainers
Young grasshopper
Reverse Proxy via nginx is no longer functional to Blue Iris, instantly throws a 502 Bad Gateway and nginx logs report the following (URLs redacted):
Directly accessing Blue Iris on LAN via
Even if i wipe the bad UA's list and add in some items such as
Edit: Yes, I populated the Host/s field, to what I assumed should be correct... the domain name, the full domain name, ip addresses, etc. - nothing worked. I've rolled back to the previous stable version until whatever issue may be ongoing is investigated and ironed out.
Code:
2026/02/26 01:07:25 [error] 1461411#1461411: *9253 upstream prematurely closed connection while reading response header from upstream, client: 192.168.20.58, server: <redacted>, request: "GET / HTTP/2.0", upstream: "http://192.168.20.7:8080/", host: "<redacted>", referrer: "<redacted>"Directly accessing Blue Iris on LAN via
http://192.168.20.7:8080/ has no issues experienced. It almost feels as if BI is expecting an additional header to be passed... Very weird behavior. UA in use: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/145.0.0.0 Safari/537.36Even if i wipe the bad UA's list and add in some items such as
perl,wget,python-requests - it makes no difference.Edit: Yes, I populated the Host/s field, to what I assumed should be correct... the domain name, the full domain name, ip addresses, etc. - nothing worked. I've rolled back to the previous stable version until whatever issue may be ongoing is investigated and ironed out.
Last edited:
CrazyAsYou
Getting comfortable
Thanks for confirming, I use nginx as a reverse proxy to remotely access BI with https, I'll hold of updating.Reverse Proxy via nginx is no longer functional to Blue Iris, instantly throws a 502 Bad Gateway and nginx logs report the following (URLs redacted):
Code:2026/02/26 01:07:25 [error] 1461411#1461411: *9253 upstream prematurely closed connection while reading response header from upstream, client: 192.168.20.58, server: <redacted>, request: "GET / HTTP/2.0", upstream: "http://192.168.20.7:8080/", host: "<redacted>", referrer: "<redacted>"
Directly accessing Blue Iris on LAN viahttp://192.168.20.7:8080/has no issues experienced. It almost feels as if BI is expecting an additional header to be passed... Very weird behavior. UA in use:Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/145.0.0.0 Safari/537.36
Even if i wipe the bad UA's list and add in some items such asperl,wget,python-requests- it makes no difference.
Edit: Yes, I populated the Host/s field, to what I assumed should be correct... the domain name, the full domain name, ip addresses, etc. - nothing worked.
Not sure why we even need this if you use a VPN? I don't get ANY connections other than my own. Just glad mine still works 
biggen
Known around here
- May 6, 2018
- 2,908
- 3,332
This. I can't fathom a reason why anyone would be hosting services without using ZeroTier or Tailscale.Not sure why we even need this if you use a VPN? I don't get ANY connections other than my own. Just glad mine still works
This. I can't fathom a reason why anyone would be hosting services without using ZeroTier or Tailscale.
It is true, you get no benefit from those security measures if you do not expose the BI web server to the internet in the first place.
But there are plenty of reasons why someone might expose their BI web server to the internet, and in such a case these additional client validations are welcome (in theory; the current implementation obviously is highly defective).
biggen
Known around here
- May 6, 2018
- 2,908
- 3,332
But you don't have to expose the BI web server to the internet if you are using either of those. It's hidden behind the VPN. You just have to connect to the VPN first via whatever client you are using (e.g. phone, tablet, etc..) to access the service.It is true, you get no benefit from those security measures if you do not expose the BI web server to the internet in the first place.
But there are plenty of reasons why someone might expose their BI web server to the internet, and in such a case these additional client validations are welcome (in theory; the current implementation obviously is highly defective).
Maybe I'm not understanding what you are saying?
CrazyAsYou
Getting comfortable
Neither of them are open source, there is price for both if you have more users/devices than the free tier allows, you're dependent on a 3rd party service, all users require another app installing on all devices they use and for them to then run/connect said app and maybe have some level of technical knowledge. Now compare that to a well setup reverse proxy adding HTTPS that is behind a well configured/maintained firewall with extra elements of WAF, IDS, geolocation, rate-limiting/banning etc etc - yes there is still some risk beyond VPN style solution but the access mgmt. is all one-sided and the user experience is much easier/better, all the users do is access the normal BI app or web address and enter their un/pw.This. I can't fathom a reason why anyone would be hosting services without using ZeroTier or Tailscale.
biggen
Known around here
- May 6, 2018
- 2,908
- 3,332
Yeah, I just know how buggy BI is. No way I would expose that program to the wilds of the internet.Neither of them are open source, there is price for both if you have more users/devices than the free tier allows, you're dependent on a 3rd party service, all users require another app installing on all devices they use and for them to then run/connect said app and maybe have some level of technical knowledge. Now compare that to a well setup reverse proxy adding HTTPS that is behind a well configured/maintained firewall with extra elements of WAF, IDS, geolocation, rate-limiting/banning etc etc - yes there is still some risk beyond VPN style solution but the access mgmt. is all one-sided and the user experience is much easier/better, all the users do is access the normal BI app or web address and enter their un/pw.
I get what you are saying, but BI isn't open source either. You could roll your own Wireguard VPN which is exactly what Tailscale is with a GUI on top of it.
But you don't have to expose the BI web server to the internet if you are using either of those. It's hidden behind the VPN. You just have to connect to the VPN first via whatever client you are using (e.g. phone, tablet, etc..) to access the service.
Maybe I'm not understanding what you are saying?
For a lot of people, locking their Blue Iris web server away behind a VPN is not a practical option because they want to be able to simply share a link and credentials with people to give them remote access without making anybody jump through the hoops of VPN client setup.
Yes, it absolutely should make you nervous to port forward directly to Blue Iris, and using a reverse proxy or Cloudflare tunnel or similar is not actually much better. I see it as a good thing that Blue Iris is making efforts to reduce the risks of this exposure.
